
Accelerating Cyber Intelligence
Cyberattacks are an extremely serious problem for safety-relevant sectors like airport operators. Like most companies, also Fraport AG, one of the leading players in the global airport business, notices a growing number of cyberattacks, resulting from security breaches. But how to handle this everyday challenge? There is a great need for innovative solutions to improve the automation of the collection as well as evaluation of relevant data from a wide range of sources on the potential vulnerabilities to revolutionize existing security systems.
#CyberVulnerabilityManagement #AIforCyberSecurity #CyberIntelligence
✅ Completed 🏁 Winner Congratulations to Tokyo AI & Protos Labs!
🏆 Prize Prize pool of EUR 5,000 + funding and collaboration programs + joint paper
🌎 Scope International - open to participants from all over the world
Specifications and desired outcome
The objective of the challenge is the implementation of an automatic import interface for security vulnerabilities and IoC, which is highly flexible in order to cope with varying source layouts from the BSI notes or other sources.
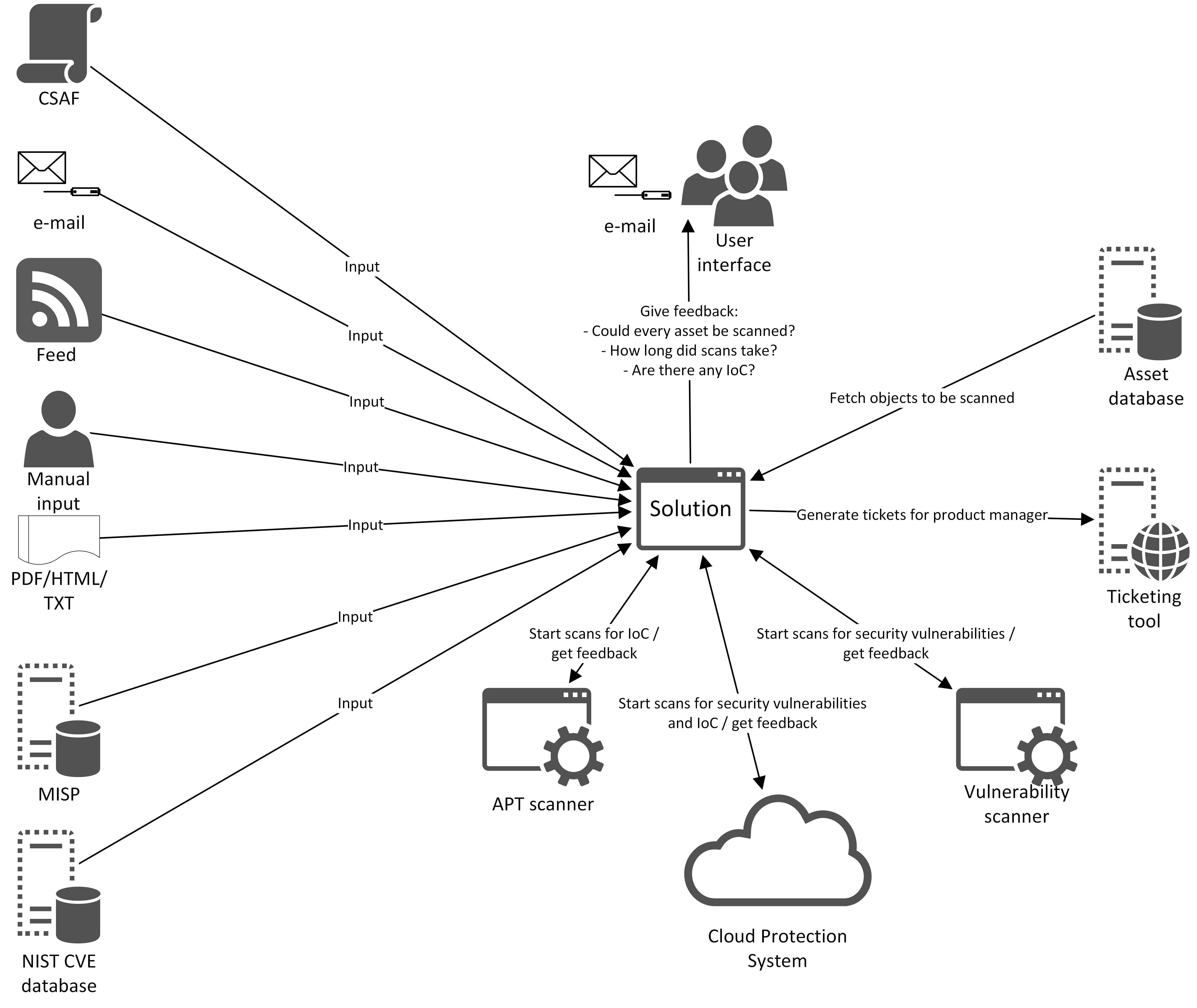
The solution must accept and handle information about security vulnerabilities and IoC from at least the following list:
- CSAF
- CVD data base (e. g. from NIST)
- MISP data base (from CIRCL)
- Mail/PDF
- Manual input
The solution must also be compatible with Fraport's asset database* to check all assets for known security vulnerabilities. The database can be accessed by a REST API. The vulnerability and APT scanner are deployed already, too. It is highly desired to implement an MVP within the six months of the program in order to evaluate the solution’s quality.
Fraport is subject to public law. Therefore, any project (viewed over the entire product lifetime) with a budget exceeding 390,000 € must be awarded as a Europe-wide public tender.
The following guidelines and capabilities can also be considered for the development of the solutions:
- Disruption response – AI-enabled systems provide enhanced context for responding to security warnings and disruptions
- Mapping of the IT Asset Inventory – full and detailed inventory of all devices, users and applications including every linked library with access to information systems
- Threat intelligence – AI-based cybersecurity systems are able to provide the latest knowledge about global and industry-specific threats
- Monitoring effectiveness – AI can be used to understand what impact the various security tools and security processes in use are having on the security posture
- User Experience – the clarity and understandability of recommendations and analysis is key to success in the use of the application. This is important to provide relevant information to all stakeholders involved, including end users, security operations, CIO, CEO, etc.
- NLP models for cognitive analysis for cybersecurity-related documents – automatically monitor the latest information relevant to cybersecurity
Please note that the participants selected to continue to the bootcamp, and elaboration phase will have to show progress and present to the Fraport´s team – depending on the approach/technology – a viable model and solution during a stage-gate decision meeting. This meeting, whose go/no-go decision will be validated by Fraport, will be decisive for the participants to pursue the Program and go to the elaboration phase. Realistic deliverables will be discussed with the participants and our teams at Fraport at the start of the Qualification phase.
*Please mind: You can find further information, such as the tool names, in the tab "Confidential Information". This tab is only visible after successful registration on the platform and challenge.